In this case, all flagged items are **false positives**.
#### Now I'm going to move on and install `RKHunter`: 1.) Install RKHunter ```bash sudo apt update sudo apt install rkhunter -y ``` 2.) Open RKHunter's Config File: ```bash sudo nano /etc/rkhunter.conf ``` Modify the following Comment this out: use Ctrl + W to search the file and then type WEB\_CMD [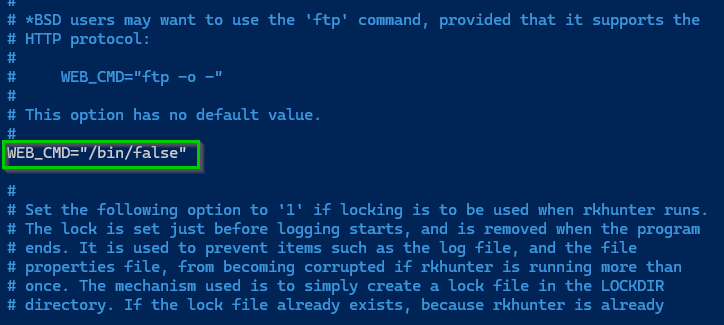](https://docs.natenetworks.com/uploads/images/gallery/2025-05/xnaIzXeXrYGVHKg0-2025-05-30-17-06-14-nathaniel-nash-all-items-1password.png) Use CTRL+W to search for UPDATE\_MIRRORS and change it to 1 [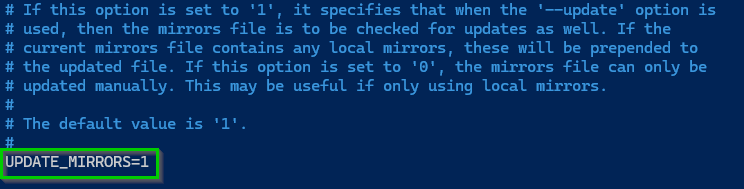](https://docs.natenetworks.com/uploads/images/gallery/2025-05/og1QpAfZglCoN7lK-2025-05-30-17-31-03-edit-page-draft-bookstack-mozilla-firefox.png) Do the same for MIRRORS\_MODE and set that to 0 [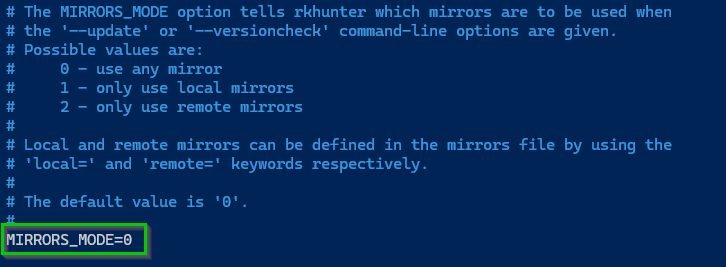](https://docs.natenetworks.com/uploads/images/gallery/2025-05/NZhyBHTQJmAkiPDK-2025-05-30-17-33-33-edit-page-draft-bookstack-mozilla-firefox.png) 3.) Update RKHunter's Data Files ```bash sudo rkhunter --update ```This pulls the latest rootkit definitions and mirror lists.
This is what you want it to look like, since it was freshly installed, nothing new was added: [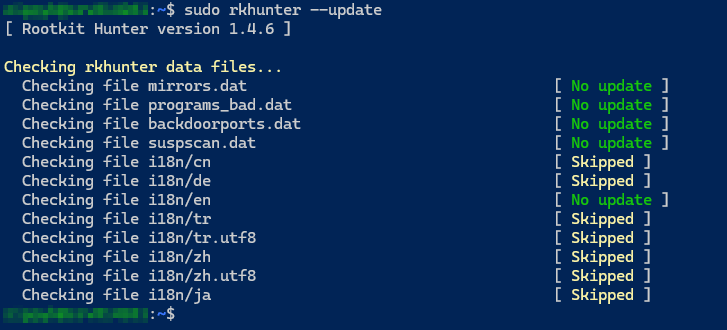](https://docs.natenetworks.com/uploads/images/gallery/2025-05/k0xb2N77325pEQsl-2025-05-30-17-34-30-edit-page-draft-bookstack-mozilla-firefox.png) Now lets run it: ```bash sudo rkhunter --check ``` It will check for possible root kits and the output should look like this: [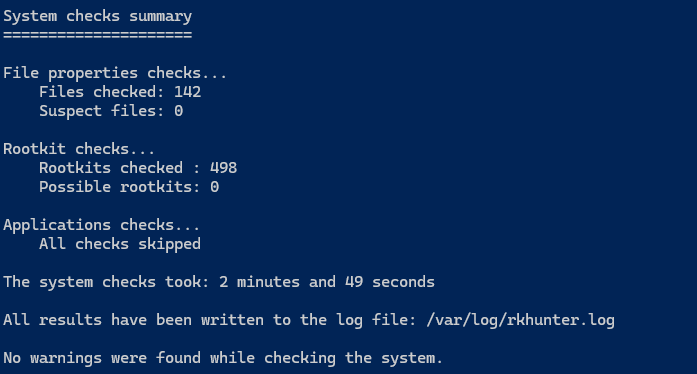](https://docs.natenetworks.com/uploads/images/gallery/2025-05/jideOtT3rV3zlP2w-image.png) Now you will have to make key presses by hitting ENTER to continue, in order to automate this we can run: ```bash sudo rkhunter --check --sk ``` or the full command: ```bash sudo rkhunter --check --skip-keypress ``` This will be useful when saving it to a logfile or scheduling it as a cron job. It runs the scan **fully unattended**. You can save the output. Allows for scripts or email alerts!